Sudo Password Enabel/Disable Sep 15, 2021
Posted by Zahid Hussain Rajput in Uncategorized.Tags: Disable sudo, Enable Sudo, GNU/Linux 11.0.0 Bullseye
add a comment
GNU/Linux Debian 11 bullseye


Following file must be configured in sudo visudo editor.
File location: /etc/sudoers in you file structure
Open your Terminal (Ctrl+T) Login as root user
$su
Enter your root password: *********
In Root terminal prompt type:
#sudo visudo /etc/sudoers
Now add the following lines to the bottom of the /etc/sudoers file and remove or add # as required read the instructions on top of each command

#if you wish to use following (Status:01) command then add # in front of Status:02 command or if you want to use Status:02 command then add # in front of Status:01 in our case we are using Status:02 and commenting out Status:01 by adding # at the beginning of the command:
# (Status:01)
# Allow only systemctl and reboot commands to run without Sudo password
#linuxconfig ALL=(ALL) NOPASSWD:/usr/bin/systemctl /usr/sbin/reboot
# Allow linuxconfig users to execute all commands without #Sudo password
linuxconfig ALL=(ALL) NOPASSWD:ALL
# Allow all Sudo members to execute all commands without any password
# if you wish to use following command add # in front of Status:01 command and
# uncomment following command by removing #
# (Status:02)
%sudo ALL=(ALL:ALL) NOPASSWD:ALL
Press
Ctrl + X to Exit
Save modified buffer?
Yes: y
No: n
Select Y to save modifications
Now your Sudo password is completely disabled you will not be asked to provide a Sudo password with every type you run the Sudo command
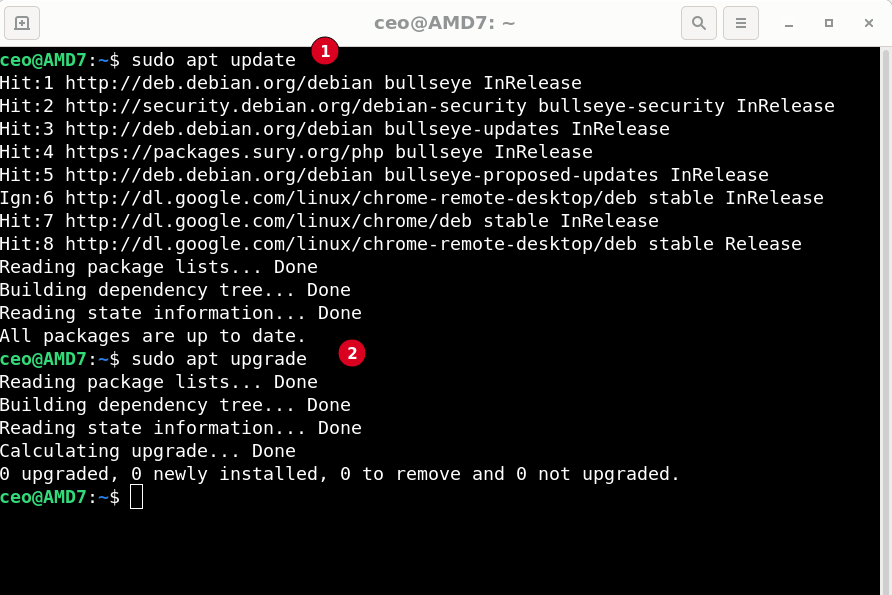
Open new terminal window and type $sudo apt update or upgrade to test your modifications
Conclusion:
This is an experimental exercise I do not recommend you to disable the sudo password from your machine because Removing the Sudo password completely is a security risk. But there are occasions where you can not complete the process while you have a sudo password enable
For example:
If you wish to add an algorithm or file to startup you need to disable sudo password for this operation in your system. In this case, add # in front of Note:02 and remove # from the front of Note:01
Once you have disabled the sudo password anyone who has access to your machine either physical or virtual can make any changes in your system so it is recommended to keep sudo password enabled in your machine.
Hope to hear your advice and suggestions in the comments
Thanks
ZHR
<<< Adding file to Startup
apt update Error Sep 10, 2021
Posted by Zahid Hussain Rajput in Linux.Tags: amd64, apt, Configure, error, file, GNU/Linux 11.0.0 Bullseye, update, upgrade
add a comment
Linux Debian 11 bullseye
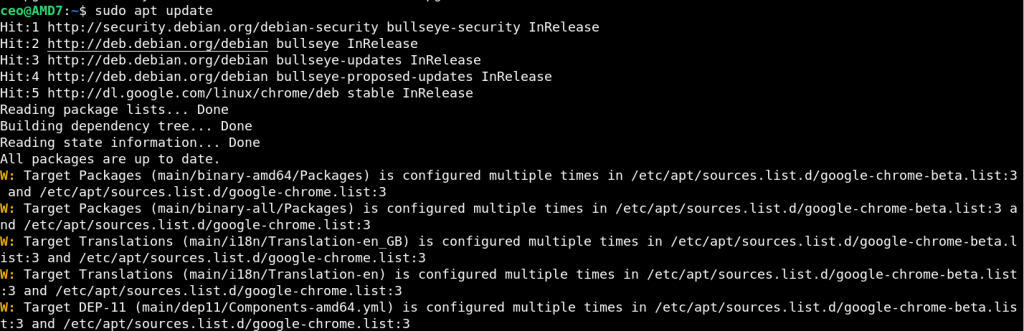
W: Target Packages (main/binary-amd64/Packages) is configured multiple times in /etc/apt/sources.list.d/google-chrome-beta.list:3 and /etc/apt/sources.list.d/google-chrome.list:3
After Installing google you might begin to get above update error, Either expediently or package you have install have Google Chrome and Google Chrome beta packages or you tried to install both at the same time as it’s mention in the error both files are conflicting with each other
Solution:
Basically /etc/apt/sources.list.d/google-chrome.list and /etc/apt/sources.list.d/google-chrome-beta.list are identical files and trying to run same process at the same time therefore either of them has to stop processing.
Open editor of your choice and edit list.d files in your system. in my case I have decide to remove/disable google-chrome-beta.list as follow:
$ sudo nano /etc/apt/sources.list.d/google-chrome-beta.list
file will open in your nano editor as follow:

Add # to disable line 3 in other word I am disabling automatically configured file you can also navigate to list.d folder and remove this file either way the purpose is served
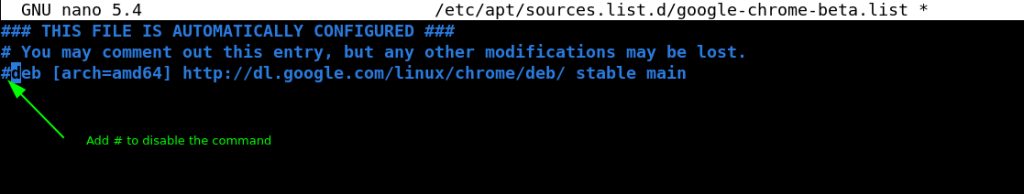
Press Ctrl + O to save file and Ctrl + X to exit editor
Now test your work by executing apt upgrade and update commands in Terminal window

Try with update command
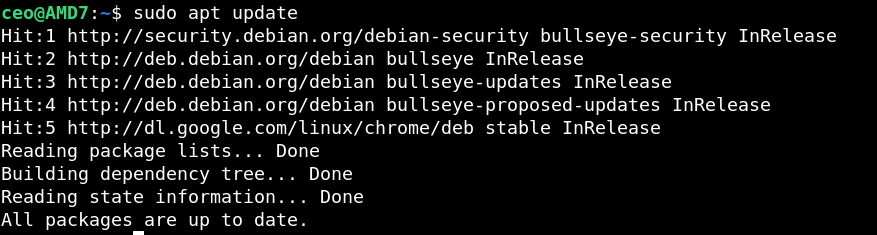
If there is two files exist in the system and serving the same purpose can conflict with each other. The easiest and only solution in my opinion is to disable one and let other use the resources of your computer. This example can be use for any conflicting file errors.
There may be other ways to resolve this issue but I find this easiest and simple and would really like to know about your experience please use comment box bellow and share your knowledge with us.
Thanks
ZHR
How to Configure apt Sep 5, 2021
Posted by Zahid Hussain Rajput in Linux.add a comment
Debian 11 bullseye
Error:
$ sudo apt update
Ign:1 cdrom://[Debian GNU/Linux 11.0.0 Bullseye – Official amd64 DVD Binary-1 20210814-10:04] bullseye InRelease
Err:2 cdrom://[Debian GNU/Linux 11.0.0 Bullseye – Official amd64 DVD Binary-1 20210814-10:04] bullseye Release
Please use apt-cdrom to make this CD-ROM recognized by APT. apt-get update cannot be used to add new CD-ROMs
Hit:3 http://deb.debian.org/debian bullseye InRelease
Hit:4 http://security.debian.org/debian-security bullseye-security InRelease
Hit:5 http://httpredir.debian.org/debian stable InRelease
Get:6 http://deb.debian.org/debian bullseye-updates InRelease [36.8 kB]
Reading package lists… Done
E: The repository ‘cdrom://[Debian GNU/Linux 11.0.0 Bullseye – Official amd64 DVD Binary-1 20210814-10:04] bullseye Release’ does not have a Release file.
N: Updating from such a repository can’t be done securely, and is therefore disabled by default.
N: See apt-secure(8) manpage for repository creation and user configuration details.
Configurations:
To resolve “apt” problem you have to edit Source file as follow:
Configuration:
Open terminal to edit source list file as follow:
$ sudo nano /etc/apt/sources.list
and comment out following line by adding # in the begining of the line:
#deb cdrom:[Debian GNU/Linux 11.0.0 Bullseye – Official amd64 DVD Binary-1 20210814-10:04]/ bullseye contrib>
Now run following apt commands
$ sudo apt update Hit:1 http://security.debian.org/debian-security bullseye-security InRelease Hit:2 http://deb.debian.org/debian bullseye InRelease Hit:3 http://httpredir.debian.org/debian stable InRelease Hit:4 http://deb.debian.org/debian bullseye-updates InRelease Reading package lists... Done Building dependency tree... Done Reading state information... Done All packages are up to date. $ sudo apt upgrade Reading package lists... Done Building dependency tree... Done Reading state information... Done Calculating upgrade... Done 0 upgraded, 0 newly installed, 0 to remove and 0 not upgraded. As you can see from our output "apt" problem is resolve for good If you think I have missed something or there is batter ways to resolve this problem please share your knowledge in comments. Thanks ZHR